TryHackMe Challenges: Sustah Room Walkthrough
TryHackMe Challenges, TryHackMeIn this post, i would like to share walkthrough on Sustah Room.

This room has been considered difficulty rated as a MEDIUM machine

Let’s Start!
We need to deploy the machine for us to play with the machine

Once the machine is fully up within 3 minutes, we can start the information gathering on the machine by executing the command nmap -sC -sV <IP Address> -PN
Information Gathering on Sustah

There are multiple ports that have been open but the crucial port that caught my attention
- 22: OpenSSH 7.2p2
- 80: Apache httpd 2.4.18
- 8085: Gunicorn 20.0.4
Let’s see what will appear on the website

Nothing that we can do right now. Let’s see a website that uses a different port 8085

Oh wow! There’s a spin button. Let’s click that button and it asks us to input a number and enter.
There are two methods of getting the number and path at the same time.
Enumerate with Burpsuite

We can see that X-RateLimit-Limit has shown on the response output.
Before we proceed, we need to know that the HTTP header has the following method:
- X-Originating-IP: 127.0.0.1
- X-Forwarded-For: 127.0.0.1
- X-Remote-IP: 127.0.0.1
- X-Remote-Addr: 127.0.0.1

Brute-Forcing the packet via Burpsuite on Sustah Room

Let’s run the intruder function to gain the path and number to proceed

It will take some time for the result to be shown here. We can test whether the number is valid or not by slapping the number on the input column and press the click button

Let’s go to the website path on the browser
MaraCMS RCE
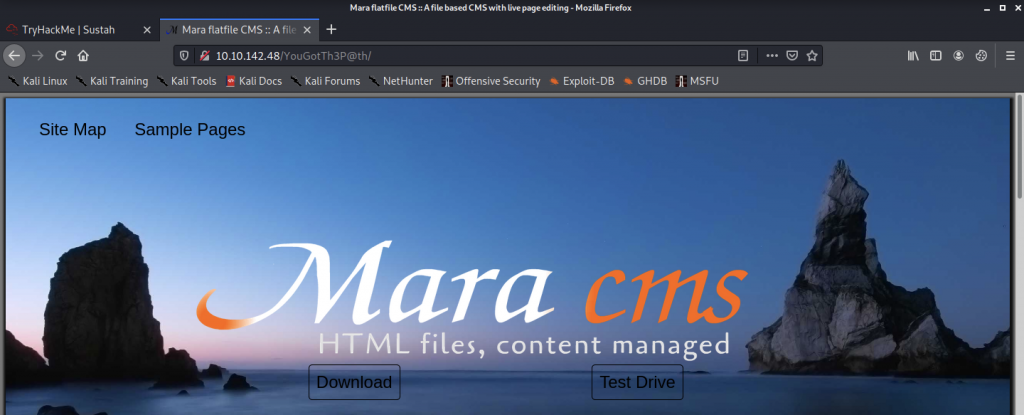
We have Mara CMS appear on the website interface. To be frankly honest, i never use Mara CMS before and let’s google to see if there’s any exploit that we can use in Mara CMS

The first result looks interesting to me and let’s see what has stored for us in the exploit


From the exploit above, I found out that we got the following information that we might be using later.
- Username: admin
- Password: changeme
- http://target/codebase/dir.php?type=filenanew
Let’s find the login page for us to login to the dashboard of Mara CMS. I will be guessing the login page path over here which <IP Address>/YouGotTh3P@th/index.php?login=
An index.php page is compulsory for most website that appears on the internet.

Wuhuu! We got the login page which we need to key-in the username and password to access the dashboard.
I have a breakdown just cracking the username and password for this website. However, i just remember that we are been provided with a username and password within the exploitdb. Let’s us try login using those credentials
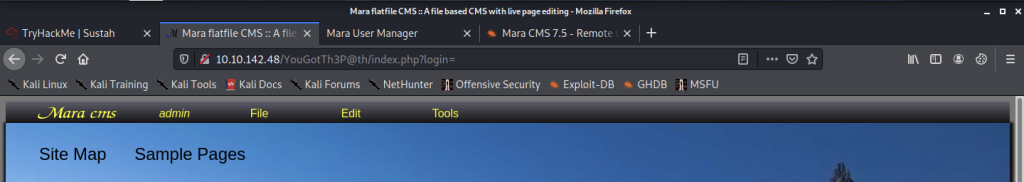
Let’s find a location to upload the reverse shell into the machine

Therefore, let’s click File>New and the website interface will look like the below:
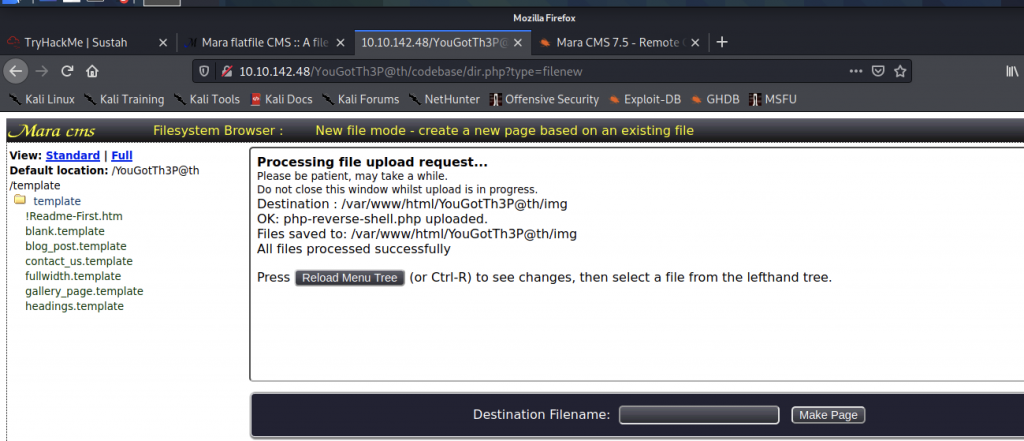
It looks like the website has been re-directed to http://target/codebase/dir.php?type=filenanew location. Let’s upload the reverse shell on the website

Before we can go to the file upload location, we need to start a listener

The website has been reloading for some time now, let’s see the listener if got the connection back.
Obtain a Reverse Shell on the machine

We have succeeded in the server environment. Let’s grab the user.txt in /home/kiran

As you can see, we cannot read the user.txt file where permission has been denied.
We need to look for kiran’s password and we can drive to /var/backups where we might find some interesting files there.


We can see the passwd.bak file which might contain the user and password that we needed.

Once again, the file permission has denied for us to read into. Let’s see if there’s any hidden file in the /var/backups

Oh wow! I found .bak.passwd in the folder. Let’s check what’s written inside that file

We have gotten kiran’s password. Let’s switch to kiran privileges access

Once we successfully have login into kiran’s privileges access, we can access to /home/kiran.
Now, we can read the user.txt below

Let’s enumerate more to access as root privileges access
We have executed some commands such as find / -user root -perms /4000 2>/dev/null and sudo -l but didn’t find anything interesting.
As a result, let’s run linpeas.sh into the machine



Now, let’s execute linpeas.sh such as below:

Once linpeas.sh have completed, i did analyze the result and found out that kiran can run rsync

Let’s go to GTFOBins and search for any exploit that we can use
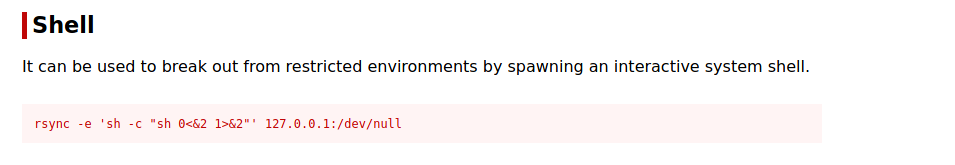
Now, let’s execute the command that we found on GTFOBins

The command doesn’t work at all, and we might need to tweak the command for it to work

And we still cannot execute it. So, let’s execute it within /var/backups

We got the bash shell on Sustah Room

Let’s read the root flag within the /root/ directory

-THE END-
Happy Learning Guys!